- doc
- anonymous internet
- Navegar per la web amb el Navegador Tor
- Servidor intermediari que rebutja connexions
- Confinament d'AppArmor, baixada i càrrega de fitxers
- Ocultar que esteu utilitzant el Navegador Tor
- Encriptació HTTPS amb HTTPS Everywhere
- Protecció contra JavaScript perillós
- Nivell de seguretat
- Circuit Tor
- Funció de Nova identitat
- NoScript per tenir encara més control sobre JavaScript
- Letterboxing
El Navegador Tor és un navegador web basat en Mozilla Firefox però configurat per protegir la vostra privadesa.
![]()
L'enviament de les vostres connexions a llocs web a través de la xarxa Tor no és suficient per protegir-vos totalment mentre navegueu per la web:
Les galetes es poden utilitzar per fer un seguiment i identificar-vos a diferents llocs web.
Les vulnerabilitats de seguretat de JavaScript s'han utilitzat per desanonimitzar el navegador Tor en el passat.
És per això que el Navegador Tor també integra tot tipus de proteccions de seguretat dins del navegador.
Algunes preguntes freqüents sobre el Navegador Tor es poden trobar a les preguntes més freqüents.
Servidor intermediari que rebutja connexions
El següent missatge d'error al Navegador Tor significa que Tails encara no està connectat a la xarxa Tor:
El servidor intermediari rebutja les connexions
Assegureu-vos que esteu:
Confinament d'AppArmor, baixada i càrrega de fitxers
El Navegador Tor només pot llegir i escriure a les carpetes següents:
- Documents
- Baixades
- Música
- Imatges
- Vídeos
- Navegador Tor
- Persistent/Navegador Tor, si teniu un Emmagatzematge Persistent
Això es deu al fet que, a Tails, el Navegador Tor està confinat amb AppArmor per protegir els vostres fitxers d'alguns tipus d'atacs contra el Navegador Tor.
Per exemple, gràcies a aquest confinament, fins i tot si un atacant aconsegueix explotar una vulnerabilitat de seguretat al Navegador Tor, no podria accedir a tot el contingut del vostre Emmagatzematge Persistent.
És per això que obteniu l'error següent si intenteu baixar fitxers a una altra carpeta:
No s'ha pogut llegir el contingut de carpeta.
S'ha produït un error en obrir el directori carpeta: permís denegat
Si voleu baixar-vos un fitxer del Navegador Tor, deseu-lo en una d'aquestes carpetes.
Si voleu carregar un fitxer des del Navegador Tor, copieu-lo primer a una d'aquestes carpetes.
Per evitar que Tails es quedi sense memòria i es bloquegi, baixeu fitxers molt grans a la carpeta Persistent/Navegador Tor. Tots els fitxers que baixeu fora de l'Emmagatzematge Persistent son emmagatzemats a la memòria (RAM), que és més limitada.
Ocultar que esteu utilitzant el Navegador Tor
És impossible ocultar als llocs web que visiteu que utilitzeu Tor, perquè la llista de nodes de sortida de la xarxa Tor és pública.
És per això que molts més llocs web us demanen que resolgueu un CAPTCHA quan feu servir el Navegador Tor.
L'anonimat proporcionat pel Navegador Tor funciona fent que tots els usuaris semblin iguals per fer impossible saber qui és qui entre els milions d'usuaris del Navegador Tor.
Tails intenta dificultar al màxim que els llocs web distingeixin els usuaris de Tails d'altres usuaris del Navegador Tor. Si fos possible que un lloc web determinés si sou un usuari del Navegador Tor dins o fora de Tails, això proporcionaria una mica més d'informació sobre vosaltres i reduiria el vostre anonimat.
Els llocs web que visiteu poden recuperar molta informació sobre el vostre navegador, ja sigui el Navegador Tor o un navegador normal. Aquesta informació s'anomena empremta digital del navegador i inclou el nom i la versió del navegador, la mida de la finestra, la zona horària, els tipus de lletra disponibles, etc.
Per dificultar la distinció dels usuaris de Tails d'altres usuaris del Navegador Tor, el Navegador Tor a Tails intenta proporcionar la mateixa informació que proporciona el Navegador Tor en altres sistemes operatius.
Una diferència és que Tails inclou l'extensió uBlock Origin, que elimina els anuncis. Si un atacant pogués determinar que no esteu baixant els anuncis inclosos en una pàgina web, això podria revelar que sou un usuari de Tails.
Per amagar a algú que controli la vostra connexió a Internet que us esteu connectant a Tor, consulteu la nostra documentació sobre connexió a la xarxa Tor.
Encriptació HTTPS amb HTTPS Everywhere
L'ús d'HTTPS en lloc d'HTTP encripta les vostres comunicacions amb el lloc web i impedeix que el node de sortida de Tor intercepti les vostres comunicacions.
Per exemple, aquí és com es veu el navegador quan intentem iniciar sessió en un compte de correu electrònic a riseup.net, mitjançant la seva interfície de correu web:
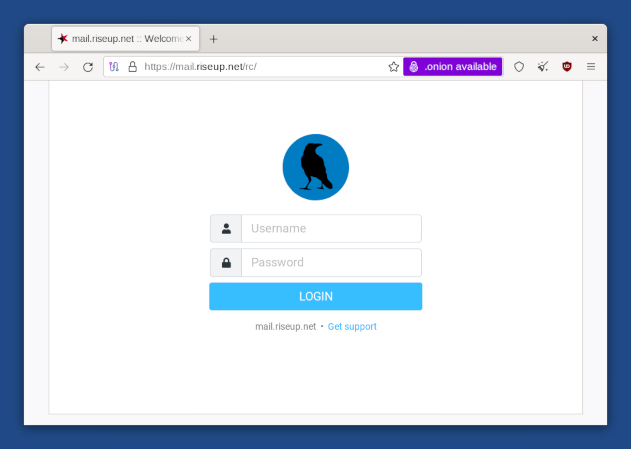
Observeu la icona del cadenat a l'esquerra de la barra d'adreces que diu "mail.riseup.net". Observeu també l'adreça que comença per "https://" (en lloc de "http://"). Aquests són els indicadors que s'està utilitzant una connexió encriptada amb [[!wikipedia_ca HTTPS]].
Quan envieu o recupereu informació sensible (com ara contrasenyes), hauríeu de provar d'utilitzar només els serveis que proporcionin HTTPS. En cas contrari, és molt fàcil per a un espia robar qualsevol informació que estigueu enviant, o modificar el contingut d'una pàgina en el camí cap al vostre navegador.
HTTPS Everywhere és una extensió de Firefox inclosa al Navegador Tor. Es produeix com a col·laboració entre The Tor Project i Electronic Frontier Foundation. Encripta les vostres comunicacions amb un gran nombre de llocs web principals. Molts llocs web ofereixen un suport limitat per a l'encriptatge a través d'HTTPS, però ho fan difícil d'usar. Per exemple, poden estar predeterminats a HTTP sense encriptar, o afegir pàgines encriptades amb enllaços que tornin als llocs sense encriptar. L'extensió HTTPS Everywhere soluciona aquests problemes reescrivint totes les sol·licituds d'aquests llocs a HTTPS.
Per obtenir més informació sobre HTTPS Everywhere, podeu llegir:
La pàgina principal d'HTTPS Everywhere (en anglès)
Les preguntes freqüents d'HTTPS Everywhere (en anglès)
Protecció contra JavaScript perillós
Tenir tot el JavaScript desactivat de manera predeterminada desactivaria una gran quantitat de JavaScript inofensiu i possiblement útil, i podria inutilitzar molts llocs web.
És per això que el JavaScript està habilitat per defecte però el Navegador Tor desactiva tot el JavaScript potencialment perillós. Considerem que això és un compromís necessari entre seguretat i usabilitat.
Per entendre millor el comportament del Navegador Tor, per exemple, pel que fa al JavaScript i les galetes, podeu consulteu el document de disseny del Navegador Tor.
Nivell de seguretat
Podeu canviar el nivell de seguretat del Navegador Tor per desactivar les funcions del navegador com a compensació entre seguretat i usabilitat. Per exemple, podeu establir el nivell de seguretat a El més segur per desactivar el JavaScript completament.
El nivell de seguretat s'estableix en Estàndard per defecte, la qual cosa ofereix la millor experiència d'ús.
Per canviar el nivell de seguretat, feu clic a la icona ![]() a la dreta de la barra d'adreces
i trieu Configuració….
a la dreta de la barra d'adreces
i trieu Configuració….
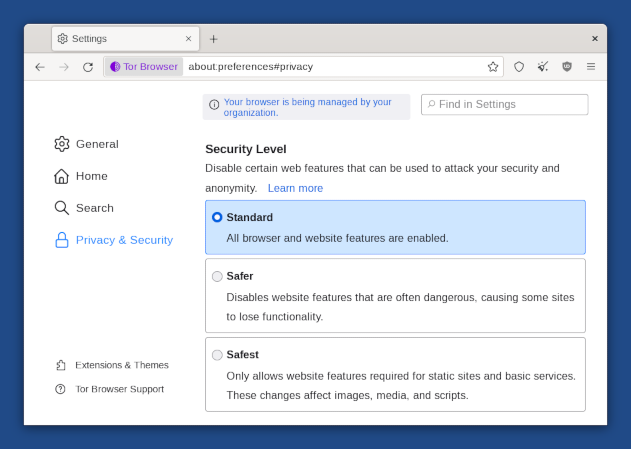
Podeu ignorar amb seguretat el missatge "El vostre navegador està gestionat per la vostra organització", que apareix a la pàgina de preferències del Navegador Tor.
Tot aquest missatge significa que la funció d'actualitzacions automàtiques del Navegador Tor s'ha desactivat. Això està fet intencionadament a Tails per assegurar-se que no hi ha cap funció o configuració de seguretat que es trenca per les actualitzacions automàtiques del Navegador Tor.
Circuit Tor
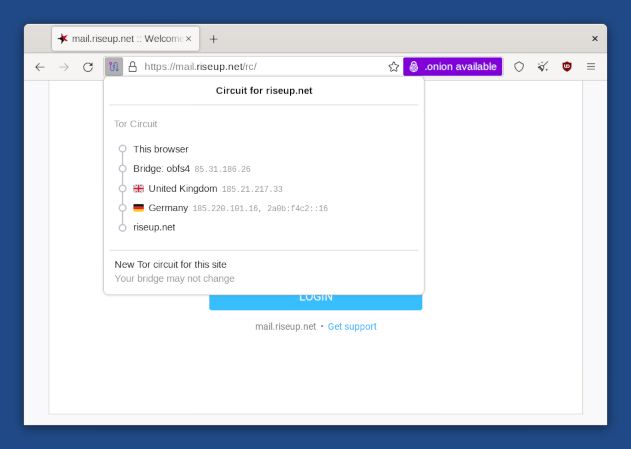
Feu clic al cadenat de la barra d'adreces per mostrar el circuit de Tor que s'utilitza per connectar-se al lloc web a la pestanya actual, els seus tres repetidors, els seus respectius països i adreces IP.
L'últim repetidor del circuit, el immediatament a sobre del lloc web de destinació, és el repetidor de sortida. El seu país pot influir en el comportament del lloc web.
Feu clic al botó Nou circuit per a aquest lloc per utilitzar un circuit diferent.
Podeu fer servir Circuits Onion per obtenir informació més detallada sobre els circuits que s'utilitzen.
Funció de Nova identitat
Per canviar a una nova identitat, seleccioneu ![]() ▸ Nova identitat.
▸ Nova identitat.
La funció de Nova Identitat del Navegador Tor:
Tanca totes les pestanyes obertes.
Esborra l'estat de la sessió, incloent la memòria cau, l'historial i les galetes.
Tanca totes les connexions web existents i crea nous circuits Tor.
Aquesta funcionalitat no és suficient per separar identitats contextuals ja que els circuits de Tor utilitzats fora del Navegador Tor no es modifiquen.
És preferible reiniciar Tails.
Per obtenir més detalls, consulteu el disseny i la implementació del Navegador Tor (en anglès).
NoScript per tenir encara més control sobre JavaScript
El Navegador Tor inclou l'extensió NoScript per:
Protegir-vos de més atacs de JavaScript. Per exemple, atacs de cross-site scripting (XSS).
Permetre-us desactivar completament el JavaScript només en alguns llocs web.
Per obtenir més informació, podeu consultar el lloc web i les funcions de NoScript.
Letterboxing
La funció de letterboxing del Navegador Tor ajuda a evitar que els llocs web identifiquin el vostre navegador en funció de la mida de la finestra. Sense letterboxing, els llocs web podrien utilitzar la mida de la finestra del navegador per fer un seguiment dels visitants o debilitar el vostre anonimat.
La funció de letterboxing del Navegador Tor funciona afegint marges grisos a la finestra del navegador quan es canvia la mida de la finestra. La pàgina web es manté el més a prop possible de la mida desitjada sense revelar la mida real de la finestra.
